Best Cyber security Course in Chandigarh
Our Cyber Security course in Chandigarh will teach you how to defend against online threats and protect systems and data. You’ll learn about key security practices, threat analysis, and incident response through practical, hands-on exercises in our Cyber Security Course in Chandigarh.
Join us in our Cyber Security Course at Netmax Technologies, Chandigarh to start your journey into cyber security!
50+ Modules Series
Earn a Certification that demonstrates your expertise.
Beginner Level
No previous experience with coding is required
5.5 months
1.5 hours/day class
Flexible Schedule
Online/ Offline both modes of classes available.
Mastering CyberSecurity Course
What you'll learn
- Default Installations
- Buffer Overflows
- Design Flaws
- Application Flaws
- Default Passwords
- Jump Cloud
- Secure link
- Immersive Labs
Cyber Security Course Overview
Introduction to Networking
What is Computer Networking?
- Types of Networks (LAN, WAN, MAN, PAN)
- Network Topologies (Bus, Star, Ring, Mesh, Hybrid)
- Client–Server vs Peer-to-Peer models
- Importance of Networking in Cyber Security
Network Models
- OSI Model (7 Layers)
- Physical, Data Link, Network, Transport, Session, Presentation, Application
- Functions of each layer with practical examples
- TCP/IP Model
- Layers and mapping with OSI model
- IP addressing and packet flow
IP Addressing & Subnetting
Introduction
- IPv4 Addressing: Classes (A, B, C, D, E)
- Public vs Private IP addresses
- Subnetting basics and calculations
- CIDR (Classless Inter-Domain Routing)
- Supernetting
- Hands-on practice: creating subnets for organizations
Networking Devices
- Switches, Routers – functionality and differences
- Access Points, Gateways, and Modems
- Packet filtering devices and network taps
Routing & Switching
- VLANs and Trunking
- Spanning Tree Protocol (STP) basics
- Routing fundamentals (Static vs Dynamic)
- Routing Protocols (RIP, OSPF, EIGRP, BGP)
- Default Gateway, Route Tables, and Path Selection
Protocols & Communication
Introduction to Protocols
- HTTP/HTTPS, FTP, SMTP, IMAP, POP3
- DNS (Domain Name System)
- DHCP (Dynamic Host Configuration Protocol)
- ARP (Address Resolution Protocol)
- ICMP (Ping, Traceroute, TTL concepts)
Wireless Networking
- Basics of Wi-Fi standards (802.11 a/b/g/n/ac/ax)
- Wireless security protocols (WEP, WPA, WPA2, WPA3)
Introduction to Linux
Introduction to Linux
- History of Linux & Open Source Software
- Difference between Windows & Linux
- Linux Distributions (Ubuntu, CentOS, Kali, Parrot OS, Amazon Linux)
- The Linux Kernel – Role and importance
- Linux File System Hierarchy (/, /bin, /etc, /usr, /home, /var, /tmp, /opt)
- Linux Boot Process (BIOS → Bootloader → Kernel → Init/Systemd)
Basic Linux Commands
Introduction to Linux
- File & Directory Navigation (pwd, ls, cd)
- File Operations (cat, touch, cp, mv, rm)
- Viewing & Editing Files (nano, vi/vim, less, more, head, tail)
- Finding Files (find, locate, which, whereis)
- File Compression & Archiving (tar, gzip, zip, unzip)
- System Info Commands (uname, uptime, hostname, whoami)
User & Group Management
- Creating & Managing Users (useradd, passwd, usermod, userdel)
- Creating &Managing Groups (groupadd, gpasswd, id)
- User Switching (su, sudo)
- Understanding UID, GID, /etc/passwd, /etc/shadow
- Configuring sudo privileges (visudo, /etc/sudoers)
File Permissions & Ownership
- Linux File Permission Model (Read, Write, Execute)
- Changing Permissions (chmod symbolic & numeric)
- File Ownership (chown, chgrp)
- Special Permissions:
- SUID (Set User ID)
- SGID (Set Group ID)
- Sticky Bit (for shared directories)
- Permission-based Practical Exercises
Linux Process & Job Management
- Debian-based (Ubuntu, Kali): apt, dpkg
- RedHat-based (CentOS, Fedora): yum, dnf, rpm
- Updating & Upgrading Packages
- Adding Repositories & PPAs
- Compiling from Source (make, gcc)
Package Management
Package Management
- Debian-based (Ubuntu, Kali): apt, dpkg
- RedHat-based (CentOS, Fedora): yum, dnf, rpm
- Updating & Upgrading Packages
- Adding Repositories & PPAs
- Compiling from Source (make, gcc)
Disk Management & File Systems
- Checking Disk Space (df, du, lsblk)
- Mounting & Unmounting Drives (mount, umount)
- File System Types (ext3, ext4, xfs, btrfs, NTFS, FAT)
- Partition Management (fdisk, parted)
- Swap Space Configuration
- Logical Volume Management (LVM Basics)
Networking in Linux
Introduction to Networking
- Configuring IP Address (ifconfig, ip addr, nmcli)
- Checking Connectivity (ping, traceroute, netstat, ss)
- Managing Network Interfaces & Routes (ip route)
- Secure Remote Access (SSH, SCP, SFTP)
- Network File Sharing (NFS, Samba)
- Firewalls (ufw, iptables, firewalld)
System Monitoring & Logs
- System Monitoring Commands (free, uptime, vmstat, sar)
- Checking Services (systemctl, service)
- Log Files in Linux (/var/log/, dmesg, journalctl)
- Analyzing Authentication Logs & Security Events
- Monitoring Open Ports & Connections
Bash Scripting & Automation
Introduction to Shell Scripting (#!/bin/bash)
- Variables, Operators, & Arrays
- Input & Output (echo, read)
- Conditionals (if, else, case)
- Loops (for, while, until)
- Functions in Bash
- Writing automation scripts:
- User creation script
- Backup automation script
- Log monitoring script
Linux Security & Hardening
- Password Policies & Account Security
- File Integrity Monitoring (AIDE)
- Disabling Root Login & Using sudo
- Configuring Firewalls & iptables rules
- Brute-force Attack Protection (Fail2Ban)
- Security Enhanced Linux (SELinux) & AppArmor
- Linux Audit Framework (auditd)
Advanced Linux for Cyber Security
- Working with Services (Apache, Nginx, MySQL, PHP on Linux)
- SSH Hardening & Key-based Authentication
- Chroot Environment for Isolation
- Container Basics (Docker on Linux)
- Linux in Penetration Testing (Kali Linux Tools)
- Linux Forensics (log analysis, recovery, timeline analysis)
Introduction to Cloud & AWS
Basics of Cloud and AWS
- Cloud Computing Concepts: IaaS, PaaS, SaaS
- Benefits of Cloud (Scalability, Elasticity, Cost Savings)
- AWS Global Infrastructure:
- Regions, Availability Zones (AZs), Edge Locations
- Shared Responsibility Model (AWS vs Customer)
- AWS Free Tier Overview
- Hands-on: Setting up AWS Free Tier Account
AWS Identity & Access Management (IAM)
- IAM Users, Groups, Roles, and Policies
- Multi-Factor Authentication (MFA)
- Access Keys & Secure AWS CLI Authentication
- IAM Best Practices for Security
- Hands-on: Creating Users, Groups, and Assigning Policies
Compute Services
Amazon EC2 (Elastic Compute Cloud):
- Instance Types & Families
- Launching & Connecting to EC2 (Linux & Windows)
- Security Groups, Key Pairs, Elastic IPs
- EC2 Storage: EBS, Instance Store, Snapshots
- Auto Scaling &= Elastic Load Balancing
- Amazon Lightsail: Simple hosting & applications
- AWS Lambda: Serverless computing, Functions, Event-driven execution
- Hands-on Labs: Launch EC2, Configure Apache/Nginx, Deploy Lambda function
Hands-On Labs & Projects
- File permission & ownership lab
- Writing bash scripts for automation
- Configuring a Linux firewall
- Setting up & securing SSH
- Linux log analysis for security monitoring
- Deploying a secure web server on Linux
AWS Storage Services
- Amazon S3 (Simple Storage Service):
- Buckets, Objects, Permissions, Versioning
- S3 Lifecycle Policies, Glacier for Archival
- Static Website Hosting on S3
- Amazon EBS (Elastic Block Store) – Volumes, Snapshots
- Amazon EFS (Elastic File System) – Shared file system for EC2
- AWS Storage Gateway Backup Solutions
- Hands-on: Hosting a static website on S3
Databases
- Amazon RDS (Relational Database Service): MySQL, PostgreSQL, Oracle, SQL Server, Aurora
- Backups, Multi-AZ, Read Replicas
- Amazon DynamoDB: NoSQL Key-Value Store
- Amazon Redshift: Data Warehousing
- Amazon ElastiCache: Redis & Memcached
- Hands-on: Deploy RDS MySQL and connect with an application
AWS Networking & Content Delivery
- Amazon VPC (Virtual Private Cloud):
- Subnets (Public vs Private)
- Route Tables, Internet Gateway, NAT Gateway
- Network ACLs & Security Groups
- Elastic IPs & PrivateLink
- Amazon Route 53: Domain Registration & DNS
- AWS CloudFront: Content Delivery Network (CDN)
- Load Balancers: Application (ALB), Network (NLB), Gateway LB
- Hands-on: Creating a VPC with Public & Private Subnets
Security & Compliance
AWS Security and Compliance
- AWS Shared Responsibility Model (Deep Dive)
- Identity Federation (SSO, Active Directory Integration)
- AWS KMS (Key Management Service) & Encryption
- AWS WAF (Web Application Firewall)
- AWS Shield (DDoS Protection)
- AWS GuardDuty (Threat Detection & Monitoring)
- AWS Inspector & Security Hub
- Hands-on: Setting up IAM, enabling GuardDuty, applying WAF rules
Monitoring & Management
- Amazon CloudWatch: Monitoring metrics, creating alarms, logs
- AWS CloudTrail: Tracking API Calls & User Activities
- AWS Config: Resource Configuration & Compliance
- AWS Trusted Advisor: Best practice checks
- AWS Systems Manager: Automation, Patching, Session Manager
- Hands-on: Create a CloudWatch Alarm for EC2
DevOps & Automation
- AWS CLI (Command Line Interface)
- AWS SDKs (Python Boto3, Node.js, Java)
- AWS CloudFormation (Infrastructure as Code)
- AWS Elastic Beanstalk (App Deployment)
- CI/CD Pipelines with AWS CodeCommit, CodeBuild, CodeDeploy, CodePipeline
- Integration with Jenkins & GitHub
- Hands-on: Deploy a web app using Elastic Beanstalk
Advanced AWS Services
- Amazon ECS & EKS: Container Management (Docker & Kubernetes)
- AWS Fargate: Serverless Containers
- Amazon API Gateway: Managing APIs
- Amazon SNS & SQS: Messaging & Queues
- Amazon Step Functions: Workflow Orchestration
- Amazon CloudFront + WAF for Secure Web Delivery
- Hands-on: Deploy containerized app using ECS
AWS for Cyber Security & Ethical Hacking
- Hardening AWS EC2 & VPC Security
- Incident Response in AWS
- Cloud Pentesting Basics (legal aspects & AWS scope)
- Logging & Monitoring for Security Incidents
- Secure S3 buckets (Avoiding Misconfigurations)
Projects & Labs
- Deploying a Multi-Tier Web Application on AWS
- Hosting a Scalable Website with EC2 + RDS + S3 + CloudFront
- Implementing High Availability using Auto Scaling & Load Balancer
- Securing an AWS Environment (IAM, WAF, GuardDuty, CloudTrail)
- Creating a CI/CD Pipeline with CodePipeline & Elastic Beanstalk
- Project: Design a Cloud Architecture for a Startup
Introduction
Introduction to Cyber Security
- What is Cyber Security?
- Support Group
Linux Setup & Introduction
- Introduction to kali Linux Course
- User Management
- Overview Kali Linux
- Installation
- Exploring newly Installed Kali
- Assignment
Kali Linux Practical -Beginners Phase 1
Kali Linux
- Info
- What is Kali Linux?
- Unix and Linux
- Why Kali?
- Downloading Kali Old
- Types of Installation
- Oracle Virtual Box
- Creating VM
- Kali Linux Terminal basics
- Exploring 300+ Commands
- Permission in Kali Linux
- Shortcuts
- Anonymity
- Proxy-Theory
- Proxy-Practical
- VPN -I
- VPN -II
- VPN -III
- TOR-I
- TOR-II
- TOR-III
- Proxy Chains
- Change IP
- Change Mac
- Macchanger
- Foot printing
- DNS Enumeration
- DNSSenum
- Brute force
- Trace DNS
- NMAP-I
- NMAP-1I
- NMAP-III
Practical -Expert Phase II
- Search exploit
- Website Foot printing
- Vulnerability Analysis
- Live Attack
- Red Hawk
- Security Audit
- Database Assessment
- Password Attack
- Plain Test to Hash
- Password Cracking
- Find my Hash
- Custom Word list
- Crunch
- Hash Generator
- Cracking Password Offline
- Password Protected zip
- THC Hydra
- Medusa
- Sniffing
- Wireshark -I
- Wireshark -II
- Wireshark -III
- Spoofing
- Ettercap-I
- Ettercap-II
- Imp info
- WPA/WPA 2
- Fern
- Metasploit
- Buffer Overview
- Honeypots
- Pent box
- Browser Exploitations Attacks
- BeEF
- SQL Inj -I
- SQL Inj -II
- Window 10
- Window 7
Extensions for Hackers
- Browser Extensions required for hackers
Enumeration
Introduction to Enumerations
- WhoIS enumerations
- Google Droking
- How to Find web Technologies
- Web enumeration Part -1
- Web enumeration Part -2
- Web enumeration Part -3
- Web enumeration Part -4
Web enumeration Part -5
Web Enumeration
- How to use Sodan
- Security Headers
- DNS recon
- NESSUS setup
- Port and CVE Scan with NESSUS
- Collect all urls from website
- Collect all urls Part -2
Subdomain Enumeration
- Source code Download
- Subdomain Enumeration
- Subdomain Part -2
Subdomain Enumeration for Subdomain Takeover
- Subjack
- Sub 404
HostileSubBruteForce
Finding Parameter
- Finding Parameter
- Parameter Brute-Force
Port Scanning
Port Scanning
- Port Scanning with Nmap
- SMB enumeration
- SSH enumeration
- SSH exploit
- SMTP enumeration
- HTTP and HTTPS enumeration
- FTP bypass
- Webserver and Enumeration and Exploitation
- Mysql port Exploitation
Web Hacking and Exploitation
- Burp-suite Setup
- Brute-force attack with Burp suite
Detect Firewall
XSS Attack
- XSS attack overview
- Stored XSS attack
- Reflected XSS attack(JSON)
- Reflected XSS attack
- Request Response with Burpsuite
- XSS automation Part 1
- DOM based XSS attack
- XSS automation with file
- XSS automation Part 3
SQL Injection Attack
- Error Based SQL Injection
- Blind SQL Injection
- Blind SQL Injection With Burp-suite and SQLmap
NoSQL Injection
- Knowledge about NoSQL
HTML Injection
- HTML Overview
- HTML Injection using HTMLiHunter
Command Injection
- Command Injection Overview
- Command Injection Basics
- Blind Command Injection
File Upload Vulnerability
- Insecure file upload
- Magic Code Bypass and file upload
IDOR
IDOR
- IDOR vulnerability
XEE attack
- XEE and XML Injection
TryHackMe Lab Solve(web)
- XSS lab
- IDOR lab
- Part 1 : OWASP Top 10 -2021
- Part 2 : OWASP Top 10 -2021
- Part 3 : OWASP Top 10 -2021
Active Directory
- Active Directory Overview
- Physical Active Directory Overview
- Logical Active Directory
Extra
- Step by Step guide VPN Setting
- How to access Hidden Internet
Description
The Importance of Cybersecurity- Safeguarding sensitive data and critical infrastructure is paramount in the digital age.
- Cybersecurity is crucial across sectors, as cyber threats and attacks continue to escalate.
- Without effective cybersecurity, organizations face risks of data breaches, financial losses, and reputational damage.

This course includes:
- 6 months duration
- Downloadable resources
- 100 % Practical
- Certificate of Completion
- ISO Cerified Institute Training
- 24 years+ Excellence
- Affordable fees
Why Join Netmax for Cyber Security Course in Chandigarh

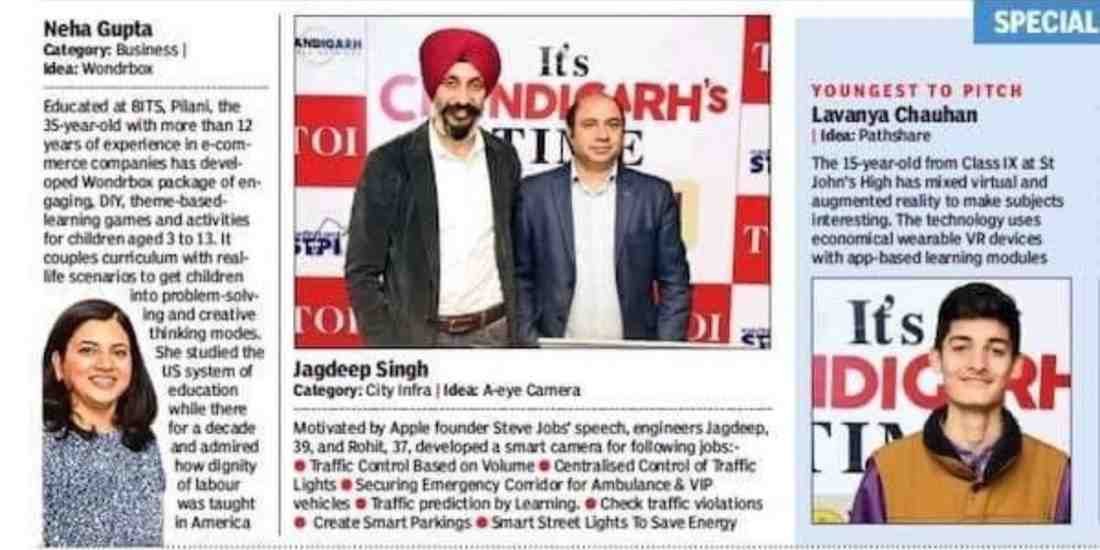
Professional Mentors
Learn Cyber Security from experts skilled in ethical hacking, network defense and real attacks.

Prepare For Certification
Get job-ready with Cyber Security practice labs, mock tests and certification guidance.

Flexible Learning Online/ Offline
Select flexible Cyber Security batches for students, beginners and working learners.

100% Practical Training
Practice Cyber Security with real labs on scanning, exploitation, forensics and defense tools.

Latest Curriculum
Learn Cyber Security topics like malware, firewalls, encryption and threat analysis.

Affordable Fees
Start Cyber Security Course with hands-on labs and job-focused training at affordable fees.

Live Expert Session
Join live expert sessions to learn real cyber attacks, defenses and security workflows.

AI- Driven Learning
Use AI tools to detect threats, analyze logs and practice Cyber Security tasks faster.
Who is this Program for?
Education
Bachelor’s degree with consistent good academic
Work Exp.
Minimum 6 Months of IT/Non-IT work experience
Career Stage
Early to Mid-Career Professionals Interested in Cybersecurity
Aspirations
Developing strong cybersecurity skills for growth
Need Free Trial Classes ??
Call us on: +91 8699644644 and take your 2 days free Demo classes
Job Assistance Program
Hands on training with real world projects . Designed for students, Freshers and working professionals
Linkdin Profile Building

Mock Interview

Resume Building Sessions

Job Assistance
Cyber Security Course Certification
Certify Your Skills
Netmax Industry-oriented Certificate validates the practical skills you have gained during training
Stand out from the competition
Add your Netmax Certificate to your resume and Linkedin profile to stay ahead of the competition
Advance in your Carrer
Share your Certification with employers to highlight your capabilities & Job ready Proficiency

Our Student's Reviews
EXCELLENTTrustindex verifies that the original source of the review is Google. I just finished my MERN Stack Web Development course at Netmax Technologies, and I’m really thankful to all the teachers for their amazing support and guidance. They explained everything so clearly and made learning fun with practical examples and projects. This course has really boosted my confidence in web development. I’d definitely recommend Netmax to anyone who wants to learn coding the right way!Trustindex verifies that the original source of the review is Google. Best institute and friendly staff will help you to learn PLC programm which will help you to grow your careerTrustindex verifies that the original source of the review is Google. Institute has good environment and faculty . It has good infrastructure as compared to other institutions for data science in sector 34.Faculty here is helpful to guide students for their future growth.Trustindex verifies that the original source of the review is Google. Nice experience learning data analysisTrustindex verifies that the original source of the review is Google. Good place must comeTrustindex verifies that the original source of the review is Google. The institute provides a well-structured and practical approach to data science. The trainers explain complex topics in a simple way, with hands-on projects that build real skills.Trustindex verifies that the original source of the review is Google. I successfully completed my Cybersecurity training at Netmax Technologies. The training was highly practical, well-structured, and focused on real-world applications. The trainers were knowledgeable and supportive, making complex topics easy to understand. This course has greatly enhanced my skills and given me a strong foundation for my career in cybersecurity. I would highly recommend Netmax Technologies to anyone looking to build expertise in this field
Our Trending Courses
Netmax Technologies Placement Assistance
We at Netmax Technology provide Job Assistance and most of the students have secure their job in various companies. We have tieups with many companies in Tricity.
Gallery




















Cyber Security Course Description
The Importance of Cybersecurity
- Safeguarding sensitive data and critical infrastructure is paramount in the digital age.
- Cybersecurity is crucial across sectors, as cyber threats and attacks continue to escalate.
- Without effective cybersecurity, organizations face risks of data breaches, financial losses, and reputational damage.
Every business today from a small startup to a large MNC is a potential target for cybercriminals. That’s not scare tactics, that’s just the reality of working in a connected world. The good news? Skilled cybersecurity professionals are in serious demand, and a cyber security course in Chandigarh at Netmax Technologies, Sector 34-A, is one of the most practical ways to step into that role.
Our course covers everything from ethical hacking and network security to malware analysis and incident response using real tools like Kali Linux, Metasploit, and Wireshark. You won’t just learn concepts; you’ll work on live scenarios that mirror what actually happens inside IT security teams. Whether you’re a student doing industrial training or a professional looking to switch into cybersecurity, this course is built to make you job-ready not just certified.
Benefits of Learning Cyber security
- Protects Data and Privacy: Gain the skills to protect sensitive information, including personal, financial, and corporate data from cyber threats.
- High Demand for Professionals: With the rise in cyberattacks, businesses worldwide need skilled cybersecurity experts to secure their infrastructure.
- Lucrative Salary Packages: Cybersecurity professionals enjoy competitive salaries due to the critical nature of their work.
- Career Flexibility: A wide range of industries, including IT, healthcare, banking, and government, require cybersecurity experts.
- Continuous Learning: The evolving nature of cyber threats means you’ll be in a field that encourages lifelong learning and staying ahead of new security trends.
- Build a Resilient System: Learn to create, manage, and safeguard systems against hacking, viruses, and malware.
Career Opportunities after completing Cyber Security Course
After Completion of this Cyber Security Course from NetmaxTechnologies, Chandigarh, you will be able to develop your career in these fields:
- Cybersecurity Analyst: Monitor and respond to security breaches in real time.
- Ethical Hacker/Penetration Tester: Legally test the security of systems to find vulnerabilities before hackers exploit them.
- Security Consultant: Provide expert advice on implementing and managing secure systems and practices.
- Network Security Engineer: Safeguard and monitor a company’s network infrastructure against unauthorized access.
- Security Architect: Design and implement security systems to protect against future threats.
- Chief Information Security Officer (CISO): Lead the cybersecurity team in ensuring robust protection across all digital assets in an organization .
Frequently Asked Questions
What is the duration of the cybersecurity course ?
The cyber security course at Netmax Technologies, Chandigarh is available for the duration of both 45 days and 3 months including 1.5 hours of classroom training and 1.5 hours of practical assignments.
What are the prerequisites for enrolling in Cybersecurity course?
For this cyber security course, there are no particular requirements. However, having a basic understanding of computers and the internet is helpful.
Is the course available online, or do I need to attend classes in person?
We provide classes both in-person and online. The format that best meets your needs can be selected.
What topics are covered in the cybersecurity course?
The course covers a wide range of topics, details of which can be found on our website.
Will I receive a certification upon completing the course?
Yes, you will receive a certification from our institute after completing the course successfully.
What practical experience will I gain during the course?
You will gain practical expertise with a range of website strategies and tools through the completion of case studies, real-world projects, and assignments.
Who are the instructors for the Cyber Security course?
Our professors are professionals in the field with years of experience. They bring practical knowledge and real-world insights to the classroom.
What kind of support will I receive during the course?
You will be able to communicate with teachers and other students in one-on-one mentorship sessions.
Do you provide career support?
Yes, we provide career support by helping in resume building, interview preparation, and job placement assistance.
How do I enroll in the Cybersecurity course?
By going to our website and completing the online registration form, you can register. As an alternative, you can come to our institute to finish the registration procedure.
What is the admission process?
Completing an application, attending a brief interview, and paying the course price are all part of the admissions process.
Are there any scholarships or discounts available?
Yes, we occasionally give out a variety of discounts. To learn more, please get in touch with our admissions office.
What kind of job roles can I expect after completing the course?
After completing a course in Cyber Security, you can pursue job roles such as AWS Engineer, Software architect, Systems administrator, AWS Cloud Architect, Cloud Developer and System engineer
Do you provide job placement assistance?
Yes, we offer job placement assistance through our network of industry partners.




